You are here: Links of Interest » HEIG-VD » Summer University 2016 » Software Reverse Engineering » Lab 2 - Hash Collisions Galore
Lab 2 - Hash Collisions Galore
This is an old revision of the document!
Table of Contents
Lab 2 - Hash Collisions Galore
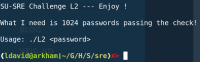
Upon its first execution the L2 binary asks the user to generate 1024 passwords. With this information we can assume than the password is not directly hardcoded in the binary but will be processed and compared against a reference value and that this process will process at least 1024 passwords to this value.
Using this assumption we can assume that the binary computes a hash of the given password and check it against a reference hash. Moreover due to the need to provide multiple passwords, we can assume that this hash function is weak against collitions.
Reverse Engineering
 The first step is to use IDA to disassemble the
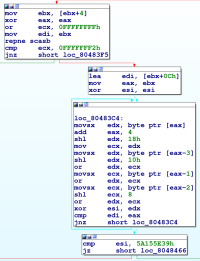
The first step is to use IDA to disassemble the L2 binary. This gives us a symbolic representation of the program's code. After analysis of the general program flow, we can see that the program looks for the presence of a single argument which we can assume is the user-supplied password. The program then checks the password (pictured left) and prints a message if the password matches an expected input.
Algorithm Analysis
The first block of code checks for the length of the string using the repne scasb instruction. This instruction is a complex instruction that decrements the ecx register while the byte at the address of the edi register is non zero. With this knowlege in mid we can infer that the program expects a password of length 0xFFFFFFFF - 0xFFFFFFF2 or 0xD16 or 1310 including the null-byte terminating the string.
